A University of Luxembourg researcher has demonstrated a new type of attack against mobile phones that allows hackers to gain control of the phones without detection (Photo: Garry Knight)
Hackers equipped with inexpensive radio hardware and open source software can compromise your mobile phone, listen to your conversations, intercept your data, or rack up huge bills on premium services, all without you knowing. Ralf-Philipp Weinmann, a cryptologist at the University of Luxembourg Laboratory of Cryptology and Security, has discovered a new type of over-the-air attack on mobile phones, and at the 2010 DeepSec conference in Vienna demonstrated how the exploit could be used against nearly any mobile phone.
Using a US$1,500 base transceiver station, Weinmann, who has previously exposed security weaknesses in the iPhone, demonstrated that common “devastating” programming errors in the Layer 3 communication stack of mobile devices can be exploited to gain control over the devices. He said that a motivated hacker could take advantage of these flaws to make an almost undetectable attack on the vast majority of cell phone models.
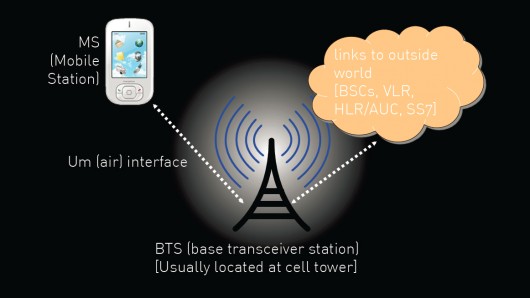
A base transceiver station is part of the cellular network that is typically found at the cell antenna site. Weinmann’s scenario calls for a cheap rogue transceiver that could be deployed in any crowded or sensitive area such as an airport, financial district, near embassies, and so on. The exploit would allow hackers to take control of mobile phones anywhere within the range of the rogue transceiver. The rogue transceiver only needs to be online for a few seconds to perform the attack.
The GSM over-the-air interface between the mobile device and the base transceiver station is called the Um interface. Layer 3 of the GSM Um interface handles connection management, mobility management, and radio resources. Weinmann’s research shows that there are many vulnerabilities in GSM baseband codebases, so it is practical to take advantage of memory corruptions over the Um interface to execute malicious code on the mobile device, compromising security.
Most service providers and customers worry about attacks against the application processor in mobile phones – nobody wants to download a virus or Trojan horse app on their smartphone. Protection against this type of attack is being built into devices by the vendors, but the baseband processor (which handles the Um interface and communications with the wireless network) has been neglected, says Weinmann. Malicious base stations are not part of the attack model that was assumed by the service providers and vendors, leaving them vulnerable.
Weinmann say that the reason for the vulnerabilities is that the baseband code base was created in the 1990s, with a 1990s attitude towards security. Network elements such as the transceiver are considered trusted devices with almost no exploit mitigation built in. He found that the Layer 3 buffers could easily be overwritten, allowing for remote code execution.
Once hackers have compromised a mobile device, they are able to monitor the user's complete communications, and could even eavesdrop on the owner by instructing the cellphone to answer incoming calls automatically without the user noticing. Other techniques might even allow the hackers to compromise the cellular base station and infect more phones from there. Detecting such hacks is difficult, as there are few built-in forensic tools in mobile devices or base stations.
Weinmann see this scenario as a developing threat. While cellular base stations are expensive, old gear and some types of new hardware such as femtocells are relatively cheap and readily available. In addition, open-source software for running GSM base stations is becoming more widely available (for example OpenBTS provided service at Burning Man from 2008 to 2010).
Weinmann and the University of Luxembourg are working together with a number of undisclosed mobile phone and cellular chipset vendors to fix the security flaws and to prevent similar flaws in the future. Weinmann says that serious code security audits and exploit mitigations by the major baseband chip vendors can go a long way toward reducing this type of security problem.
Copyright © gizmag 2003 - 2010 To subscribe or visit go to: http://www.gizmag.com