Online Marketplaces Sell Stolen eBay and PayPal Credentials
By Kenneth Corbin
EcommerceBytes.com
December 24, 2012
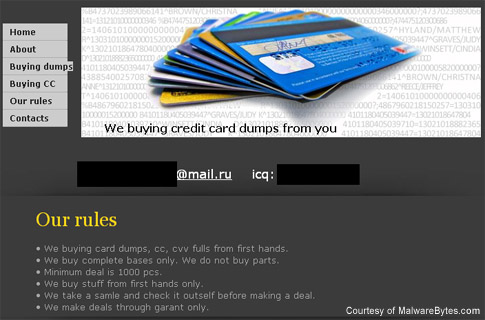
| Jerome Segura, a senior security researcher with the vendor
Malwarebytes, has
recently been researching these sites, many of which operate
underground on an invitation-only basis, though an alarming
number are publicly available, including some hosted in the
United States, Canada and the United Kingdom.
Segura's research adds a layer of understanding to a phenomenon that's hardly new - criminals have been swiping and selling credit card numbers for decades. But he took to his company's blog last week to issue a fresh warning for users to take steps to minimize their risk, including keeping anti-malware programs up to date to prevent keyloggers or other Trojans from installing themselves and snagging login credentials to bank accounts, Facebook, eBay or any number of other online services. "It's a pretty widespread problem. It's nothing new per se," Segura said in an interview. "In terms of timing, more people are going to be making purchases around the holidays, so we thought it would be a good idea to remind people that particular malware, specifically keyloggers, are around these days." "All of us make purchases online, and you'd be amazed how quickly it can be stolen," he added. Many of the sites Segura analyzed - a microcosm of the overall online black market, to be sure - operate with a surprising degree of professionalism, incorporating many of the popular features that have made legitimate online shopping such a hassle-free experience, including customer support, fluid money movement, shopping carts and easy checkout. Many of the sites even offer return guarantees. Segura explained that in this underground world of stolen personal and financial information, the sellers still compete with one another on the same factors that buyers look for in above-board retailers: reliability, price, service and reputation. "It's a real ecommerce platform," Segura said. "A lot of it is being able to guarantee that what you have for selling is accurate and current. ... I think they're trying to make sure their customers are happy." "As much as everybody - buyers and sellers - are criminal, they have a common interest." The sites typically do a bulk business. One site Segura examined recently dumped upwards of 10,000 PayPal accounts onto its marketplace, for instance. Pricing generally ranges from $1 to $4 per account, whether it's an eBay or PayPal credential or a credit card. "It was a lot lower than I expected," Segura said. But then again, there is a high likelihood that most of the credentials for sale will not be valid by the time a buyer tries to use them. So while sellers actively seek out fresh stores of account information, the caveat emptor precept seems to imply for buyers that a great portion of any batch of credentials they purchase will be worthless, hence the low per-item price. Similar to legitimate online payment services, buyers of stolen credentials will typically preload value onto an account, commonly using an e-money service called Liberty Reserve that Segura described as "loose" on verification. Though many of the black-market sites are run out of countries with weak laws or slack enforcement against Internet crimes, others operate in nations with fairly advanced law enforcement regimes. But it is common for them to routinely shift their domain names, and some are kept on an invitation-only basis, where access is negotiated on underground forums. Malwarebytes researchers routinely alert Internet hosts of these criminal sites, but Segura said that they often will not return calls and emails, preferring instead to turn a blind eye and keep a paying customer. Some researchers, though not Segura, at least in this case, work actively with law enforcement officials to help bring down online criminal rings. But it's a game of whack-a-mole, especially with the identity marketplaces, which so often shut down one name only to resume operations under another. In addition to maintaining up-to-date anti-malware software, Segura urges users to ensure they employ a different set of identity credentials for each online account. About the Author |
|
You may quote up
to 50 words of any article on the condition that you attribute
the article to EcommerceBytes.com and either link to the
original article or to www.EcommerceBytes.com. All other use is prohibited. |