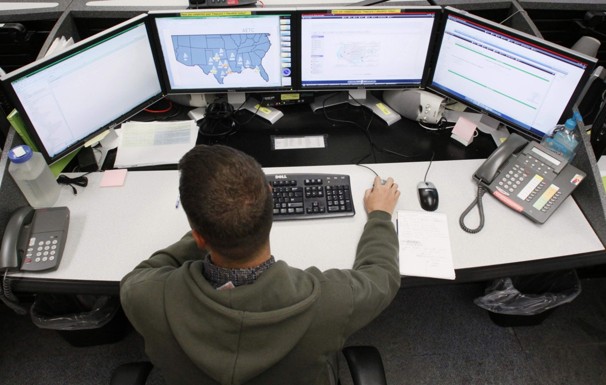
RICK WILKING/Reuters -
A network defender works at the Air Force Space Command
Network Operations & Security Center in Colorado Springs,
Colorado. The Pentagon is expanding efforts to safeguard
critical computer systems and conduct cyberattacks against
foreign adversaries, officials say.
The Pentagon
has approved a major expansion of its
cybersecurity force over the next several years,
increasing its size more than fivefold to
bolster the nation’s ability to defend critical
computer systems and conduct offensive computer
operations against foreign adversaries,
according to U.S. officials.
The move, requested by the head of the
Defense Department’s Cyber Command, is part of
an effort to turn an organization that has
focused largely on defensive measures into the
equivalent of an Internet-era fighting force.
The command, made up of about 900 personnel,
will expand to include 4,900 troops and
civilians.
Details of the plan have not been finalized, but the
decision to expand the Cyber Command was made by senior
Pentagon officials late last year in recognition of a
growing threat in cyberspace, said officials, who spoke
on the condition of anonymity because the expansion has
not been formally announced. The gravity of that threat,
they said, has been highlighted by a string of sabotage
attacks, including one in which a virus was used
to wipe dat a from more than 30,000
computers at a Saudi Arabian state oil company last
summer.
The plan calls for the creation of three types of
forces under the Cyber Command: “national mission
forces” to protect computer systems that undergird
electrical grids, power plants and other infrastructure
deemed critical to national and economic security;
“combat mission forces” to help commanders abroad plan
and execute attacks or other offensive operations; and
“cyber protection forces” to fortify the Defense
Department’s networks.
Targeting ‘malicious actors’
Although the command was established three years ago
for some of these purposes, it has largely been consumed
by the need to develop policy and legal frameworks and
ensure that the military networks are defended. Current
and former defense officials said the plan will allow
the command to better fulfill its mission.
“Given the malicious actors that are out there and
the development of the technology, in my mind, there’s
little doubt that some adversary is going to attempt a
significant cyberattack on the United States at some
point,” said William J. Lynn III, a former deputy
defense secretary who helped fashion the Pentagon’s
cybersecurity strategy. “The only question is whether
we’re going to take the necessary steps like this one to
deflect the impact of the attack in advance or . . .
read about the steps we should have taken in some
post-attack commission report.”
Although generally agreed to by the military’s
service chiefs, the plan has raised concerns about how
the Army, Navy, Marines and Air Force will find so many
qualified cybersecurity personnel and train them. It
also raises deeper issues — which are
likely to intensify as the Cyber Command grows over the
years — about how closely the command should be aligned
with the National Security Agency, the giant
electronic-spying agency that provides much of its
intelligence support.
The head of the Cyber Command, Gen. Keith B.
Alexander, is also the director of the NSA, which
employs some of the nation’s most advanced
cyber-operations specialists.
The new force structure was alluded to last fall in a
major speech by Defense Secretary Leon E. Panetta,
who said, “Our mission is to defend the nation,” and noted that
the department was “putting in place the policies and
organizations we need to execute the mission.”
In an interview, a senior defense official said that the
“national mission” teams would focus their efforts overseas and
that any actions they took would be directed outside U.S.
networks — unless the teams were asked to provide assistance to
another agency with domestic authority, such as the FBI.
“There’s no intent to have the military crawl inside industry
or private networks and provide that type of security,” the
official said.
He stressed that the military would act only in cases in
which there was a threat of an attack that could “really hurt,”
adding: “We’re not talking about doing something to make sure
that Mrs. Smith’s bank account didn’t get hijacked by somebody.”
The plan to expand the Cyber Command comes at a time when the
military’s services are being ordered to cut spending, a
reflection of how important senior military officials consider
the need to improve the nation’s cybersecurity footing. Some
military officials have grudgingly accepted the need to
contribute personnel to an expanded cybersecurity force. There
are also differences over how much control the combatant
commands will have over cyber teams.
The “combat mission” teams may help commanders in operations
such as a cyber component to disable an enemy’s
command-and-control system before a conventional attack. Each
region will have teams that focus on particular threats — say,
from China or Iran.
“You get the resource guys sucking a lot of air through their
teeth because they know their service chiefs have backed it,”
one Navy official said. “So they have to find the resources to
pay for the people.”
Alignment with NSA
Some military and defense officials question whether the
Cyber Command can reach its full potential as a military command
as long as it is so dependent on the NSA and is led by the NSA’s
director. The close relationship between the two
has had its advantages, officials say: The agency can peer into
foreign networks and provide the command with intelligence,
including in cases in which an adversary is suspected of
planning a computer attack or developing a potent virus.
“That gives you an advantage of being able to plan for and be
prepared to react,” the defense official said.
But the NSA is so intertwined with the Cyber Command — the
two operations centers are located side by side, and, until
recently, some Cyber Command personnel had nsa.gov e-mail
addresses — that some current and former officials wonder
whether the military command can create an independent,
strategic doctrine. The concern is that the intelligence
agency’s priorities will dominate, with an emphasis on the
development of tools that are useful for surveillance but not
necessarily for disrupting adversaries.
There’s a “cogent argument” to be made that for the Cyber
Command to become a true military command, “you sever that”
relationship, one military official said.
But, in fact, said one former intelligence official, the NSA
uses military personnel to do much of its work and pays for a
good portion of the services’ cyber operators. “That’s been the
plan all along,” the former official said. “Take the talent
resident in NSA, turn it into [cyber] attack talent.”
With the decision to expand the Cyber Command, Alexander, who
has been asked to stay on until summer 2014, is seeing some of
his vision fulfilled. He has sought independent budget authority
for the Cyber Command to hire and control forces, similar to the
way Special Operations Command can. He has not won that
authority, though officials agreed to give him the additional
forces. He also has the support of senior Pentagon officials to
elevate
the Cyber Command to full command status, out from under the
aegis of Strategic Command. But that move, which requires
consulting with Congress, is not happening just yet, officials
say.
http://www.washingtonpost.com/world/national-security/pentagon-to-boost-cybersecurity-force/2013/01/19/d87d9dc2-5fec-11e2-b05a-605528f6b712_story_1.html