'Massive' Locky ransomware campaign targets hospitals
FireEye researchers have spotted a surge in cyberattacks on hospitals in the US -- and they're using a new infection technique.
By Danny Palmer |

Hospitals have become a lucrative target for hackers.
A massive cybercriminal campaign is targeting hospitals with the notorious Locky ransomware, using a new technique to infect systems with the file-encrypting malware.
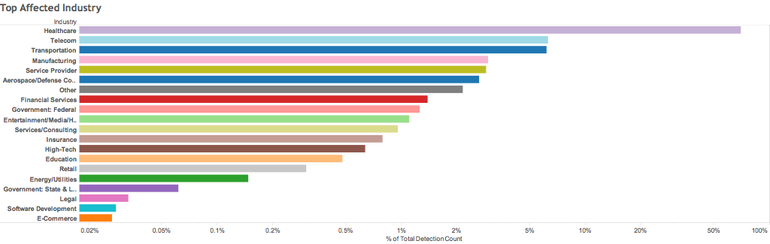
Security researchers at FireEye observed a spike in the number of attempts to deliver Locky during the first half of August, with hospitals accounting for over half the instances in which hackers attempted to infect a user with a ransomware payload.
Hospitals are an appealing target for cybercriminals to infect with ransomware not only because of the crucial role of IT in healthcare, but also because the data held by hospitals is so vital.
Earlier this year, a Los Angeles hospital paid a $17,000 Bitcoin ransom after a Locky infection took down its network.
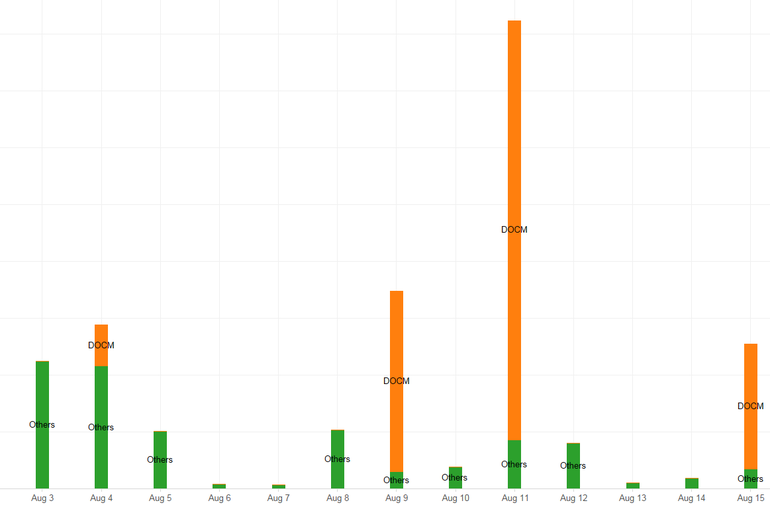
At that time it was a JavaScript-based downloader sent by email which was predominantly used to infect victims, but now hackers are starting to use a different sort of file to deliver the ransomware payload: DOCM files, the macro-enabled file used in Microsoft Word.
Researchers spotted a massive amount of phishing emails between August 9 and August 15 that attempted to deliver this Locky campaign, with an exceptionally large spike in attempts on August 11. The malicious attachment was sometimes accompanied by a message stating that someone else had asked finance files to be forwarded on.
This particular campaign targeted organisations across the globe but focused mostly on the US, Japan, and South Korea.
FireEye researchers note that the number of Locky ransomware downloaders is increasing and that the hackers are constantly changing their tools and techniques, so web users must remain vigiliant to avoid becoming yet another Locky victim.
"These latest campaigns are a reminder that users must be cautious when it comes to opening attachments in emails or they run the risk of becoming infected and possibly disrupting business operations," says FireEye researcher Ronghwa Chong.
Cybersecurity researchers and the authorities have both warned about the increasing threat of ransomware to corporate and public sector networks.
http://www.zdnet.com/article/a-massive-locky-ransomware-campaign-is-targeting-hospitals