This is the first ever reported
real-world case in which criminals
played smart in such a way that they
used BTS — a piece of equipment usually
installed on cellular telephone towers —
to spread malware.
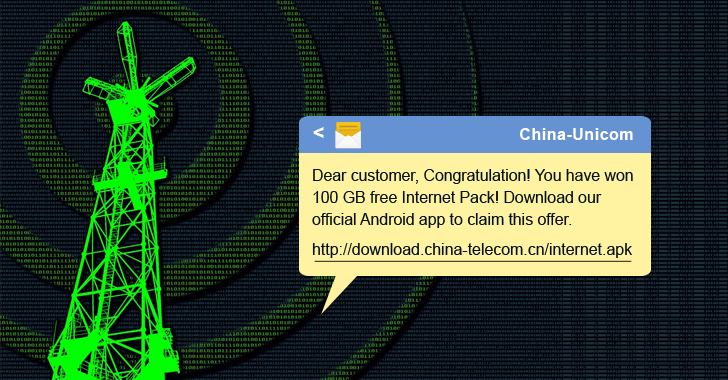
The phishing SMS, which masquerades
itself as the one coming from Chinese
telecom service providers China Mobile
and China Unicom, contains very
convincing text with a link to download
malicious Android APK.
Since Google Play Store is blocked in
China, the SMS easily tricks users into
installing the APK from an untrusted
source.
"Using a BTS to send fake messages
is quite sophisticated, and the SMS
content is very deceptive. The
message tricks users into clicking a
malicious URL which installs
malware," the researchers said in
the
blog post.
Once installed, the Swearing malware
distributes itself by sending automated
phishing SMSes to a victim's contacts.
However the maximum range of a BTS
antenna may be as low as 10-22 miles,
the technique is very successful and
sophisticated in targeted attacks.
Discovered last year by Tencent Security
researchers, the Swearing Trojan has the
capability to steal bank credentials and
other sensitive information from victim
Android devices and to bypass two-factor
authentication by replacing a user's
legit SMS app with a malicious version
that intercepts incoming SMS messages.
What's more interesting? To avoid
detection of any malicious activity, the
Swearing trojan doesn't connect to any
remote command-and-control (C&C) server.
Instead, it uses SMS or emails to send
stolen data back to the hackers.
"This provides the malware with good
cover for its communications and
hinders attempts to trace any
malicious activity."
While this particular malware campaign
has usually targeted Chinese users,
Check Point researchers warned in a blog
post that the threat could quickly
spread worldwide when adopted by Western
malware.
The malware scheme seems to be larger
than previously thought, as according to
researchers, only 21cn.com email
addresses were used in the initial
malware campaign, while new attacks used
other popular Chinese email service
providers, such as 163.com, sina.cn, and
qq.com, and Alibaba Cloud and other
cloud service hosted email accounts as
well.
Check Point also points out the nasty
HummingBad malware trojan that was also
discovered in the Chinese mobile market,
and "turned out to be early birds which
continued to spread worldwide" if
adopted by western malware.